Why universities must become flexible lifelong partners, not one-time providers — from timeshighereducation.com by Sankar Sivarajah
As careers become increasingly non-linear and shaped by rapid change, universities must evolve beyond traditional degree provision, says Sankar Sivarajah. Here, he outlines strategies
From programmes to learning ecosystems
These pressures point towards a broader redefinition of higher education. Rather than viewing education as a one-time experience culminating in a degree, universities increasingly need to see themselves as partners in professional development across an entire career.
This means moving from a model centred on programmes to one focused on learning ecosystems that allow individuals to enter, leave and re-engage with higher education as their needs evolve.
Business schools may be particularly well placed to lead this shift because of their close engagement with employers and their long tradition of educating professionals at different stages of their careers.
But success will depend on more than introducing new modules or certificates. Universities must confront a fundamental question. Are the systems, structures and cultures that define higher education capable of supporting genuinely flexible learning?
The sector has already embraced the language of lifelong learning – the next step is ensuring that universities themselves are built to deliver it.
From DSC:
Long-time readers of this blog have seen this graphic of mine posted over the last 12+ years:
.
.
Also relevant/see:
What if the undergraduate journey were a four-year internship? — from timeshighereducation.com by Michelle Seref
Treating work placements and co-curricular programmes as optional or supplementary misses deeper questions about whether traditional degrees prepare students for careers. Michelle Seref explains
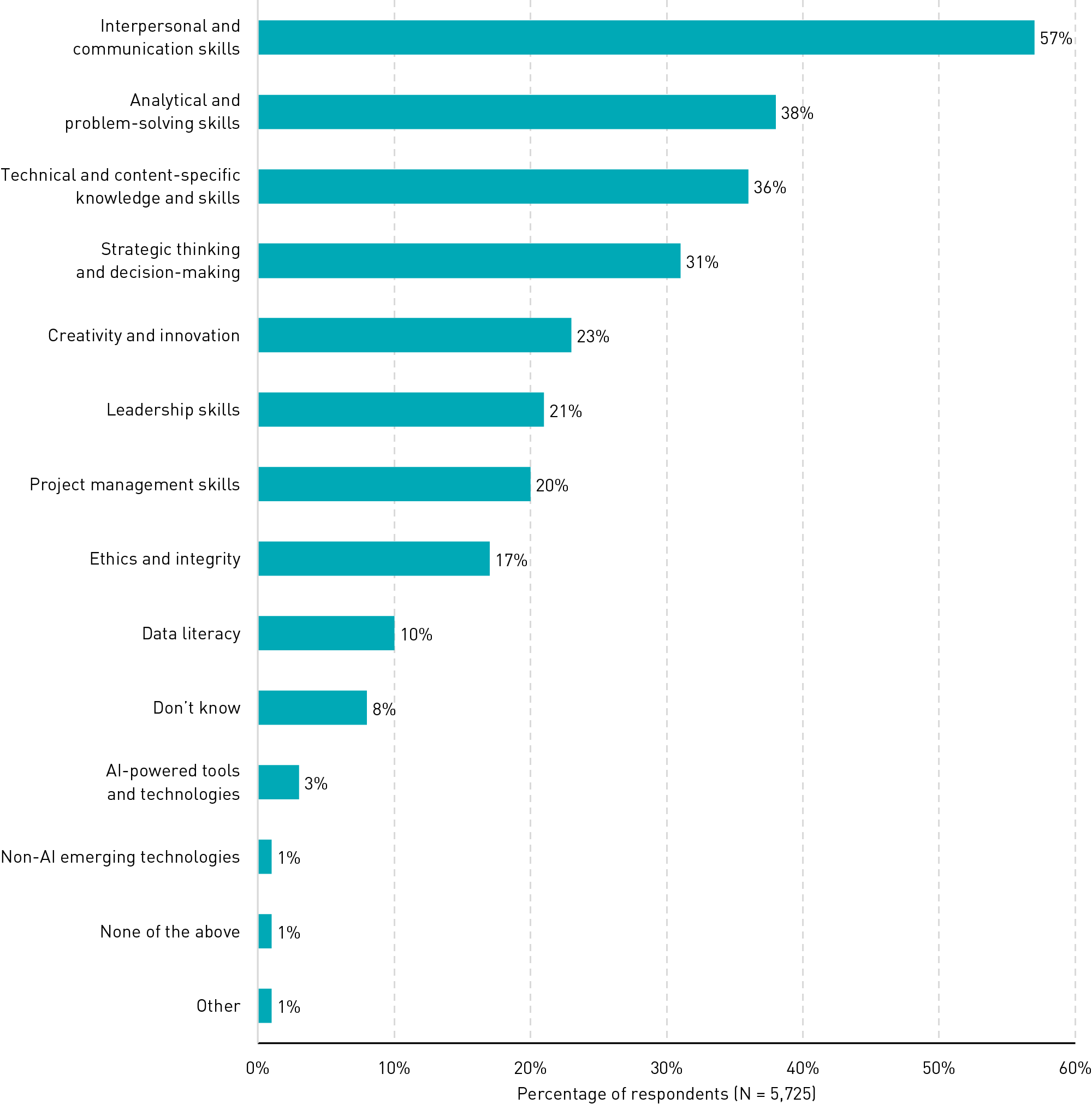
Attending workshops or polishing a résumé in their final semester does not make students career-ready. They need to practise how to work – how to collaborate, navigate ambiguity, manage projects and apply knowledge in context – throughout their academic experience. The reality is that career readiness is not a co-curricular programme; it is an essential part of an integrated curriculum.
To be clear, employers do not expect classrooms to become training centres. What they are asking for – implicitly and explicitly – is graduates who can function in complex environments from day one. That means graduates who can work in teams, communicate professionally with stakeholders, adapt when plans change, apply theory to real constraints and learn continuously on the job.
These capabilities do not develop through passive learning. But experiential learning is often misunderstood as a single, high-impact activity: an internship, a capstone project or study abroad. In reality, its power comes from repetition and progression. One experience introduces exposure. A sequence of experiences builds competence.
We are proposing a paradigm shift: repositioning the undergraduate journey as a four-year professional internship rather than a continuation of the K-12 classroom environment.
.
From DSC:
The problem with this innovative idea is that faculty often are not out in the “real world.” The best chance higher ed has to deliver on this idea is via the adjunct faculty members out there. Often, they are the ones practicing what they are teaching. They are constantly pulse-checking — and actively involved with — their industries and have more up-to-date, practical knowledge.
But this is a problem for traditional institutions of higher education, which have treated their adjunct faculty members poorly through the years. Adjunct faculty members hardly make minimum wage, have no benefits, no retirement plans, etc. — plus they have little to no say in faculty senates.
Organizational change would be a requirement.